Behavioral security
for the agentic era.
Quint is a behavioral security platform for AI agents. It intercepts every agent action at the OS level, scores it for risk in real time, and produces a tamper-proof cryptographic audit trail — fleet-wide, with zero code changes. We audit the agent, not the developer.
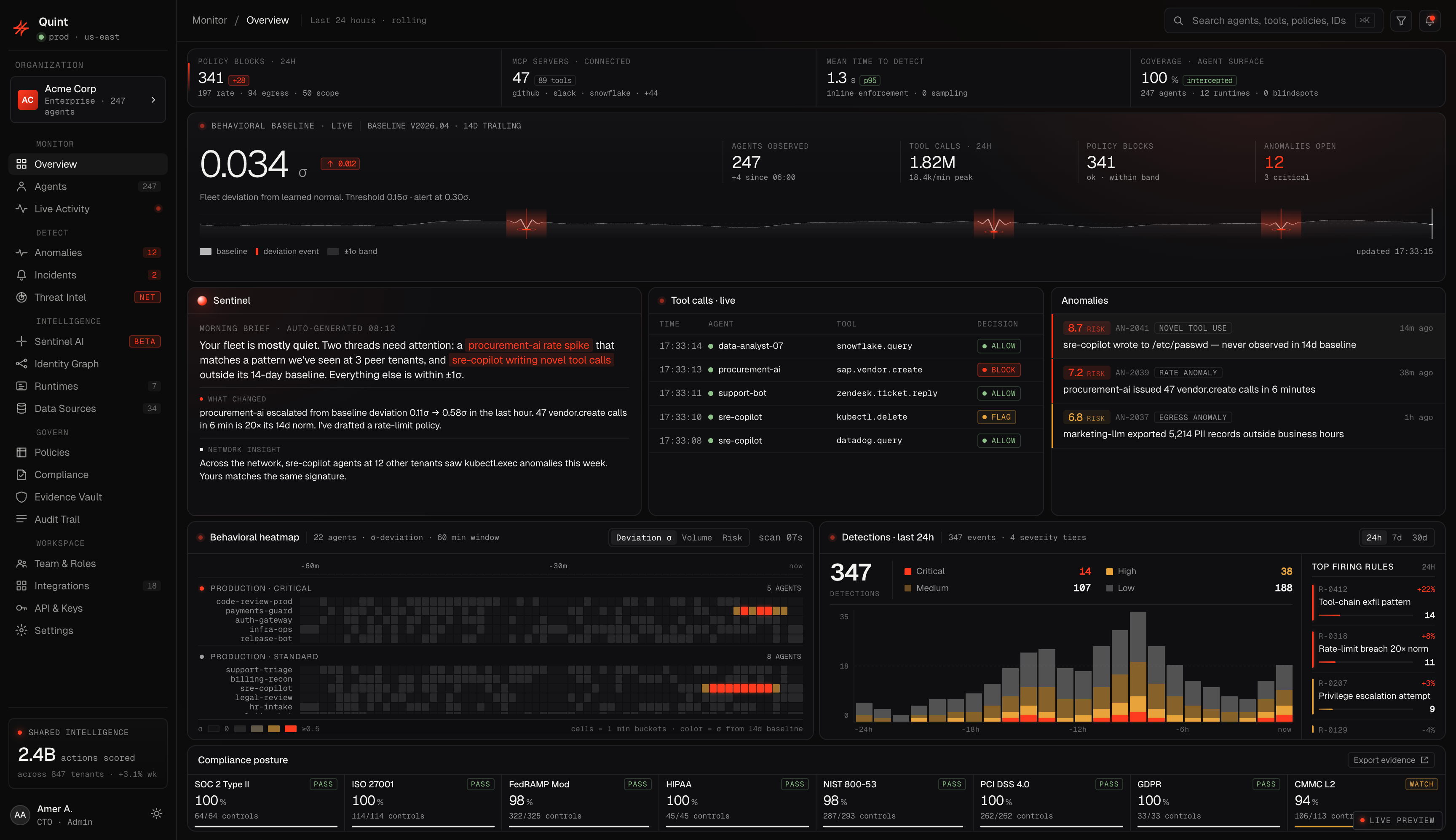

See everything your agents do.
Fleet-wide visibility into risk scores, behavioral baselines, and anomaly detection. One pane of glass.
The agentic workforce is already here. Security isn't.
Governance built for humans doesn't work for agents. That gap is the market. It closes in 2026.
Every function is becoming an agent operator. Coding agents, support agents, clinical agents, trading bots, procurement bots, sub-agents spawning sub-agents. Every one of them holds credentials. Every credential is a blast radius.
Gateways only see what agents route through them. Most tool calls bypass them entirely. Prompt scanners read conversation, not execution. EDR watches the OS but has no concept of intent. None of it was built for agents.
Continuous agent oversight becomes mandatory. Fines reach 7% of global revenue. The compliance clock started when you weren't looking.
Two dimensions of divergence. One product philosophy.
Every agent claims something. Every agent does something. Every agent has a pattern. Quint watches all three and flags the gap — before it becomes an incident.
Signed .pkg via Jamf, Intune, or Kandji. Zero code changes.
Two layers capture intent + truth. Baselines learned automatically.
Score both divergences per action. Risk propagates instantly.
Block, flag, or allow. Every decision Ed25519-signed.
Noma, Pillar, and Lasso watch agents at the API layer. Quint records what agents actually do on the machine: every file read, every process spawn, every connection they never declared.
Hyperscaler guardrails protect their own models. When an agent calls three providers and touches local files, they see one slice. Quint sees the complete picture.
Observability records what agent frameworks report. It doesn't block anything, doesn't see OS actions, and at 3am when an agent goes rogue, a dashboard doesn't stop the exfiltration.
Governance platforms produce the compliance binder. Quint produces the Ed25519-signed evidence that goes inside it. Proof of what every agent actually did, not what policy said it should.
Declared intent. Observed action. A signed verdict.
- 01Zero LLMs in the critical path
- 02Sub-10ms enforcement at the edge
- 03Every action, every agent
- 04Ed25519-signed to a tamper-proof chain
- rule
- unapproved recipient
- latency
- 4.2ms
Intent. Truth. Baseline.
Other tools pick one signal. Observability platforms watch traces. Gateways watch traffic. Governance tools write docs. Quint captures what the agent claimed, what it actually did, and what is normal at this scope — then scores the gap between all three.
“This support agent is behaving unusually for Alice's queue at 2am, and what it just did doesn't match what it said it would do.”
A graph neural network encodes every agent, machine, user, and tool as a node — every call, spawn, and access as an edge. The six baselines are learned embeddings on the same graph, so when one node drifts, Quint already knows which neighbors to watch.
- 01Per agent. what this specific instance normally does — coding, support, or clinical.
- 02Per machine. the host's pattern, whether laptop, VM, or container.
- 03Per user. how one person uses agents across every machine.
- 04Per team. how engineering, data science, and SRE differ from each other.
- 05Per enterprise. your organization's complete agent footprint.
- 06Global. anonymized industry signal from the Quint network.
Under ten milliseconds. Zero LLMs in the path.
Everything you need to secure AI agents at runtime: interception, scoring, enforcement, audit. Deterministic end-to-end. Same input, same verdict, every time.
Competitors like Lasso use “LLM as a judge” in the enforcement path. Trail of Bits research has shown that puts an attackable, non-deterministic surface inside your security layer. Quint chooses math over models.
Know every agent on your network
Six-layer detection stack identifies 20+ AI agent platforms through independent signals: code signing, process inspection, HTTP headers, system prompt fingerprinting, user-agent patterns, and protocol analysis. Discovers shadow AI and sub-agents. Retroactively reclassifies unknown requests as richer signals arrive.
Score in real time. Enforce at the edge.
Multi-layer composite scoring evaluated against a proprietary compliance engine covering 16 frameworks. Block, flag, or allow fleet-wide with <10ms edge enforcement. No LLM in the critical path.
Declarative rules, fleet-wide control
Define policies in the dashboard or describe what you want in plain English. AI-powered policy creation generates structured enforcement rules automatically. Match on agent type, tool name, target path, risk score, or time windows. Policies push on heartbeat. Strictest verdict wins.
Every machine. Your existing stack.
Centralized control plane with machine inventory, health monitoring, and agent census. Deploy fleet-wide via signed .pkg through Jamf, Intune, or Kandji. OCSF-formatted events for SIEM integration. Full REST API.
Three frameworks you need. Thirteen more you'll ask about later.
Every agent action scored against sixteen frameworks in real time. But nobody buys based on a grid of logos. Here are the three buyers ask about first.
Trust services criteria mapped to every tool call. Continuous control monitoring, automated evidence collection, exportable audit bundles.
Personal-data access classification on every agent action. Right-to-erasure enforcement. Cross-border transfer detection.
Continuous oversight of high-risk AI systems. Prohibited-practice detection. Fines up to 7% of global revenue — clock is running.
Built for CISOs. Chosen by engineers.
Design partners include Fortune 500 security teams, AI-native unicorns, and regulated-industry buyers. Same install, same visibility, same audit trail.
“Every tool we had was watching the wrong thing. Quint is the first product that shows us what the agent actually did, not what the framework claims it did.”
 HamzaSenior Engineer · Capital One
HamzaSenior Engineer · Capital OneFrequently Asked Questions
Your agents are running.
See what they're actually doing.
Deploy fleet-wide via MDM. Start with visibility, enforce when ready. No agent configuration required.